Today’s enterprise environments rely heavily on machine identities— a subset of Non-Human Identities—to power automation, cloud services, and application interactions. However, these identities are often poorly managed, exposing organizations to significant security and operational risks.
This blog unpacks machine identity management, why it’s essential, and how to apply best practices to reduce risk and improve operational efficiency. We’ll also show how Clutch Security helps teams secure machine identities using a Zero Trust approach tailored for NHIs.
What is Machine Identity Management?
Machine identity management refers to the processes, technologies, and policies used to manage machine identities—including API keys, service accounts, tokens, digital certificates, secrets, and more. The goal is to ensure a streamlined and secure machine identity lifecycle, maintain compliance, and reduce security risks. Effective machine identity management supports operational efficiency and enables continuous, secure communication between applications, devices, virtual machines and services.
Machine Identity Management as a Core Component of NHI Security
Machine identities, which are one subset of NHIs, also include bots, scripts, and autonomous applications. Managing their sheer volume, speed, and diversity requires more than just tracking them. It demands a smart, policy-driven approach. With clear policies and automated controls governing their lifecycle and usage, organizations can reduce risk, strengthen security posture, and meet compliance requirements—all while keeping up with the speed of modern development. Without effective machine identity management, security hygiene breaks down, attackers find their way in, and operational stability is at risk.
Machine Identity Management vs. Machine Identity Security
While machine identity management focuses on the full lifecycle of identities, machine identity security ensures they are protected from misuse and unauthorized access. Both are essential pillars of a strong identity and access management (IAM) strategy.
| Aspect | Machine Identity Management | Machine Identity Security |
| Primary Focus | Managing the lifecycle of machine identities from creation to revocation | Protecting machine identities from misuse, unauthorized access, or compromise |
| Key Activities | Provisioning, deprovisioning, rotation, inventory tracking | Continuous monitoring, access validation, risk mitigation, and anomaly detection |
| Goal | Ensure every machine identity is properly issued, updated, and retired | Ensure every machine identity is used securely - only accessing authorized resources and performing legitimate operations |
| Tools or Capabilities Typically Used | Vaults, secret managers, inventory tools | Risk and posture management, Threat detection, Zero Trust controls |
| Scope | Operational lifecycle control | Security enforcement and real-time risk and threat mitigation |
| Responsibility | Often managed by IT or DevOps teams | Typically owned by Security, IAM, or SecOps teams |
| End Result | A well-organized, properly managed inventory of identities with strong hygiene and no unnecessary identities | Reduced attack surface and minimized risk of identity misuse |
Why is Machine Identity Management Important?
Without structured machine identity management, organizations face:
- Increased Attack Surface: Machine and non-human identities outnumber human identities, often holding high privileges. Unmanaged, orphaned, or over-permissioned identities become low-hanging fruit for attackers. Poor hygiene also enables privilege escalation and lateral movement.
- Compliance Risks: Regulations like GDPR and frameworks like NIST require machine identity governance. Compliance gaps lead to audit failures, fines, and reputational damage.
- Operational Disruptions: Expired certificates or misconfigured machine access controls can break critical processes, affecting business continuity and agility.
- Operational Inefficiency: Stale or unnecessary identities clog up your environment, consuming time and resources needed for regular audits, access reviews, and manual clean-up efforts.
How Does Machine Identity Management Work?
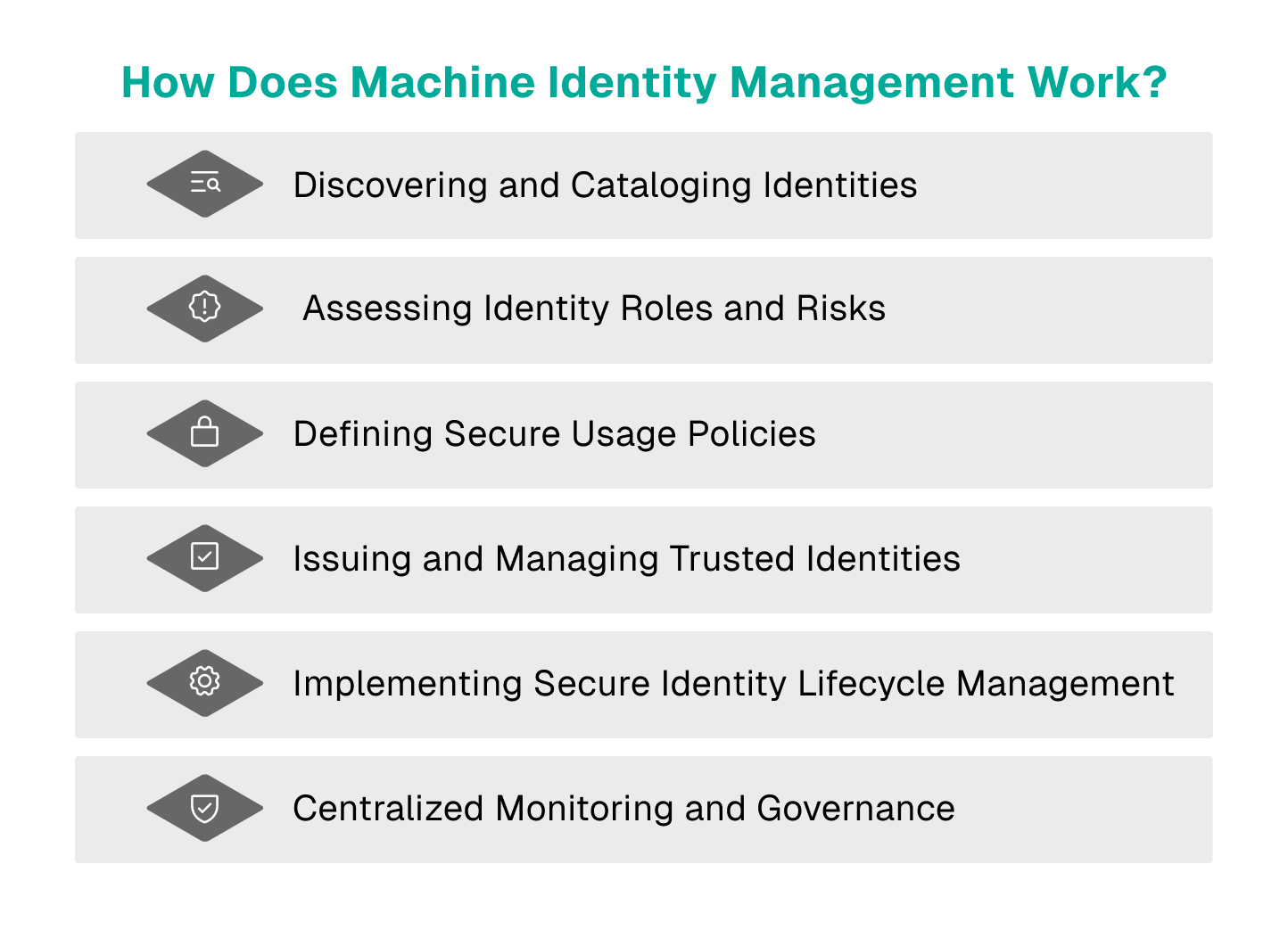
1. Discovering and Cataloging Identities
The first step is gaining comprehensive visibility into all machine identities that exist across your environment. This includes identities in:
- Cloud platforms (e.g., AWS IAM roles, Azure Managed Identities, GCP Service Accounts)
- On-premises systems (e.g., service accounts in Active Directory, internal certificates)
- SaaS applications (e.g., OAuth tokens for third-party integrations)
- Code repositories (e.g., embedded API keys or credentials in GitHub, GitLab)
- CI/CD pipelines (e.g., build service identities used by Jenkins, GitHub Actions)
- Secrets management vaults (e.g., HashiCorp Vault, AWS Secrets Manager)
Why This Matters:
Without full visibility, orphaned or stale identities can linger undetected, providing attackers with a perfect entry point. Discovery should be automated and continuous—this is not a static asset inventory.
2. Assessing Identity Roles and Risks
Once discovered, each machine identity must be classified based on:
- Its role (e.g., database backup service, deployment automation identity)
- The data or resources it can access (e.g., sensitive data stores vs. internal logs)
- Its privilege access level (e.g., read-only vs. admin)
- Usage frequency and lifecycle stage (e.g., long-lived or short-lived, active or dormant)
This classification helps prioritize risk—for example, a service account with access to production databases deserves closer attention than an ephemeral CI/CD identity for dev environments.
3. Defining Secure Usage Policies
Once machine identities are classified, security teams must establish clear and automated policies that dictate how each type of identity can be used. This includes:
- Enforcing least privilege for all identities (only the minimum permissions needed)
- Defining approved use cases for each identity type (e.g., API keys should never be used for interactive logins)
- Implementing geofencing rules (limiting machine identity use to specific regions or environments)
- Setting expiry requirements for different identity classes (shorter for higher-risk identities)
Why This Matters:
Without clear and enforceable usage policies, machine identities can be overused, misused, or repurposed in ways that violate security best practices—leading to privilege creep and increased attack surface.
4. Issuing and Managing Trusted Identities
Provisioning new machine identities should follow a standardized, auditable process. This includes:
- Verify ownership assignment (every identity should have a named owner)
- Issuing identities through approved channels (e.g., automated workflows integrated with your secrets management system)
- Embedding security controls at the creation
- Logging the issuance event for future audits
5. Implementing Secure Identity Lifecycle Management
Machine identities should never be “set and forget.” Effective lifecycle management ensures that every machine identity is either automatically revoked if unused for a predefined period or promptly deprovisioned when it’s no longer needed—such as when a project ends, an application is retired, or a vendor relationship is terminated. In addition, machine identity ownership should be verified and reassigned or revoked whenever the assigned owner leaves the organization. This prevents orphaned identities from accumulating over time, closing off an often-overlooked attack vector.
6. Centralized Monitoring and Governance
The final (and ongoing) step is ensuring that all machine identities are continuously monitored and governed from a central platform. This includes:
- Maintaining a centralized inventory that tracks the full machine identity lifecycle—from issuance to retirement
- Real-time monitoring for anomalies
- Audit logging all identity usage and changes
- Detecting and alerting on policy violations (e.g., machine identities used from unauthorized regions)
Why This Matters:
Machine identity sprawl is real. Without centralized governance and access management, you’ll end up with blind spots where identities go unmanaged, opening the door to unauthorized access, compliance violations, and operational surprises.
Tips from the Expert: Strengthening Machine Identity Governance
A common mistake in machine identity security is failing to map out the full lifecycle of machine identities, from creation to decommissioning. Without structured governance, identities accumulate excessive privileges, remain active beyond their intended use, or are left unmonitored, creating high-risk attack vectors.
Actionable Tips:
- Implement an Identity Inventory & Ownership Model: Establish an ownership structure where every machine identity is linked to a responsible team or individual. Maintain a centralized registry that logs:
- Identity type (service account, API key, digital certificate, etc.)
- Issuance date & expiry status
- Last usage timestamp
- Privilege level & access scope
- Set Expiration Policies for All Non-Human Identities:
- Short-lived credentials: Use ephemeral tokens and enforce automatic expiration
- Long-term credentials: Implement automated revocation policies for unused or orphan identities
- Monitor for Anomalous Behavior. Deploy behavior analytics to detect:
- Identities accessing new or unauthorized resources
- Excessive API calls or unusual authentication patterns
- Machine identity reuse across different workloads/environments (a key indicator of identity theft)
By treating machine identity management as an ongoing security function, rather than a one-time setup, organizations can reduce privilege creep and maintain continuous compliance.
Zero Trust for Machine Identities
Applying Zero Trust principles to machine identities ensures that every machine identity is continuously validated before accessing any resource. This real-time trust check is essential for preventing misuse—even if credentials leak.
Solutions like Clutch’s Zero Trust Protection enforce granular controls that ensure legitimacy before granting access.
Examples of Machine Identity Management
Machine identity management spans across cloud platforms, CI/CD pipelines, and SaaS integrations. In cloud environments, it covers service accounts, IAM roles, and API keys. CI/CD pipelines rely on ephemeral tokens, while SaaS apps use OAuth tokens for integrations. Internal infrastructure depends on digital certificates for secure machine-to-machine communication. Effective management ensures these identities are properly governed, monitored, and retired when no longer needed—reducing both risk and operational overhead.
Benefits of Machine Identity Management

- Strengthened Cybersecurity Posture: Protects against diverse threats: credential theft, supply chain attacks, and insider misuse.
- Reduced Risk of Unauthorized Access: Enforces least privilege and limits lateral movement if credentials are compromised.
- Automated Credential Lifecycle: Automates discovery, issuance, management, and retirement—reducing errors and improving efficiency.
- Simplified Regulatory Compliance: Ensures auditable control to meet industry standards and regulations.
- Enhanced Operational Efficiency: Prevents disruptions from expired certificates and misconfigured identities, reducing manual audits.
Challenges of Machine Identity Management
| The Challenge | What It Means | Why It Matters |
| Limited Visibility into Identities | Organizations don’t know how many machine identities exist or where they are. | Blind spots let attackers exploit unmanaged or forgotten credentials. |
| Inconsistent Policy Enforcement | Each platform has its own identity rules and controls. | No consistent governance, increasing risk of misconfigurations. |
| Securing Public and Private Keys | Keys are often hardcoded, left unrotated, or poorly stored. | Exposed keys can lead directly to data breaches. |
| Fragmented Certificate Management | Certificates are not tracked centrally. | Expired or misconfigured certificates disrupt operations and create security gaps. |
| Compliance and Regulatory Hurdles | Regulations demand strong identity governance. | Weak controls lead to audit failures, fines, and reputational damage. |
| Downtime and Service Disruptions | Expired identities or broken access disrupt critical processes. | Service outages impact business continuity and customer experience. |
| High Operational Costs | Manual discovery, management, and auditing are time-consuming and error-prone | Security and DevOps teams lose time to manual work instead of strategic projects and scale |
| Manual Oversight of Identity Governance | Identity governance relies too much on human review. | Increased risk of errors, missed reviews, and stale identities creating long-term risk. |
Machine Identity Management Best Practices
- Enforce Least Privilege Access and Conduct Regular Audits: Limit machine identities to the minimum permissions necessary for their specific tasks. Regularly review and audit permissions to detect and remove excess privileges before they become security liabilities.
- Implement Strong Credential Management: Store all secrets, API keys, and certificates in secure vaults—never hardcoded in code repositories, configuration files, or logs. Rotate credentials when necessary, but recognize that rotation alone is not a reliable defense. Attackers operate faster than rotation cycles, and over-reliance on rotation creates a false sense of security. Instead, adopt a Zero Trust mindset and continuously validate identity usage.
- Strengthen Security with Advanced Authentication: Where possible, replace static credentials entirely with federated identities and short-lived, purpose-bound credentials. Layer in Zero Trust controls—continuously monitor identity behavior, validate usage in real-time, and enforce policy-driven authentication for every identity action.
- Standardize Identity Governance: Establish clear policies that govern the creation, usage, rotation, and retirement of machine identities across all environments—from cloud platforms to SaaS tools to on-prem systems. Standardized governance reduces policy drift and prevents gaps.
- Centralize Identity and Certificate Management: Maintain a single, authoritative inventory of all machine identities, including their origin, purpose, ownership, storage, privileges, and lifecycle stage. Centralizing this machine identity data gives security teams visibility and control across fragmented environments.
- Leverage Automation for Efficiency: Use automation to discover, classify, and monitor machine identities continuously. Automated workflows can enforce policies, alert on misconfigurations, and even deprovision unused identities—reducing both risk and operational burden.
- Build Internal Expertise and Training: Equip security, DevOps, and infrastructure teams with ongoing education around machine identity risks, governance best practices, and emerging threats. Internal expertise ensures teams make informed decisions and reinforces a culture of security-first identity management.
How to Automate Machine Identity Management
Automation reduces risk by ensuring machine identities are consistently managed and monitored, and is essential for managing machine identities at scale. Start by automatically discovering and inventorying all NHIs across cloud, SaaS, code, CI/CD, and on-prem systems. Use policy-driven provisioning and deprovisioning to enforce least privilege and eliminate stale identities. When possible, shift to ephemeral credentials that expire automatically, reducing reliance on manual management and revocation. Add real-time and continuous monitoring and anomaly detection to catch suspicious behavior fast. Finally, centralize visibility and governance through a single platform, giving security teams continuous oversight without relying on manual audits.
How Clutch Enhances Machine Identity Management and Security
Clutch Security delivers a purpose-built platform to solve the complex challenges of managing and securing machine and non-human identities.
- Complete Visibility and Context: Clutch provides a centralized view of all NHIs across all landscapes, eliminating blind spots and delivering detailed context for comprehensive oversight.
- End-to-End Lifecycle Management: From creation to retirement, Clutch automates NHI governance to ensure least privilege, timely decommissioning, and consistent management.
- Risk Identification and Guided Remediation: Clutch continuously assesses NHI posture, prioritizes risks, and offers actionable remediation playbooks to accelerate response.
- Robust Threat Detection: Clutch detects suspicious activity in real-time to quickly identify and prevent misuse or unauthorized access before it escalates into incidents.
- Zero Trust Controls: Clutch extends Zero Trust principles to NHIs by ensuring continuous monitoring and validation of every NHI interaction.
With Clutch, organizations gain control over machine identity sprawl, improve compliance, reduce risk, and free security teams from manual work—all through a unified, automated platform.
Conclusion
As organizations scale, machine identity management becomes a critical component of cybersecurity. Ensuring secure machine identities through automation, Zero Trust frameworks, and centralized governance reduces security risks and enhances operational efficiency.
By implementing best practices and leveraging identity-first security solutions like Clutch, organizations can effectively manage and protect machine identities across diverse IT environments.